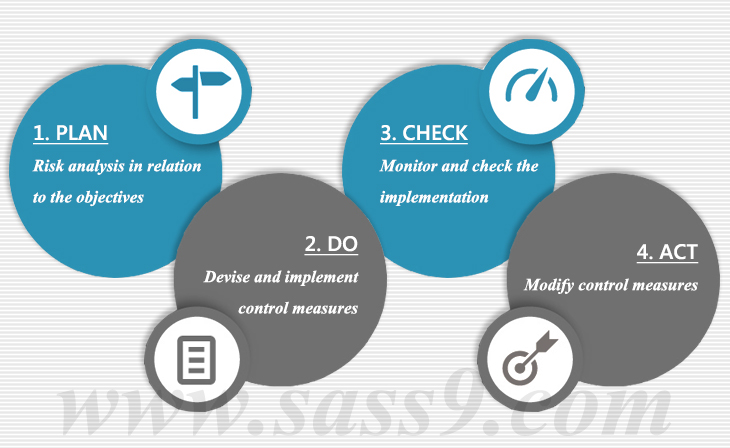
ACAT has the mnemonics that says Avoid, control, accept and transfer, this ACAT plan is an integral part of our premium services. It is an all-around security program where we access most of the possible areas from where a threat can enter into the system. We check out all the vulnerability areas with great precision and marshal all our resource in the direction of this threat removal. It is an illustrated plan where we introduce some planned control measures. These control measures are applicable to all the layers of our security blanket.
Impact analysis is yet another area where we specialize, as a part of our risk management plan; we also access the possible impacts of various threats. We develop some deceptive techniques in order to fool the attackers. We did a great deal of paperwork behind this exercise; this paperwork enables us to pass on the job to new teams all the times. This rotation policy also enables us to see loopholes from a different point of views. It is a framework in black & white and implementation in red letters in our key that enables our Risk analysis and Risk management plan.